Without a doubt, most businesses encounter attacks in one form or another. Threats evolve in tandem with technology and become increasingly sophisticated due to the availability of new tools – and the immutability of human error. After experiencing an incident, ransomware recovery is a complex and costly procedure for businesses. The coping strategy is the same as with most threats: immunity is better than mending everything after the damage is done.
Ransomware has been around for quite some time, but it remains one of the biggest risks for organizations. Moreover, it can be downright fatal to smaller businesses. For this reason, having preventative measures in place can be crucial for minimizing the chances of disastrous outcomes.
The history of ransomware began 35 years ago with the AIDS Trojan, which continues to be one of the most significant cyber threats today. In this blog, we will look into ransomware recovery and everything there is to know about pre – and post-attack scenarios for organizations. Join us for this read.
Why having a ransomware recovery strategy is crucial for businesses
Having complex and extensive prevention and recovery strategies can be vital for an organization in case of a ransomware attack. Even for businesses that are well-informed about the risks, an attack can be disastrous or even fatal. Staying informed about the threats and knowing what to expect can help prepare better for a potential attack and significantly speed up the ransomware recovery, saving your business money.
What is a ransomware attack, and what does it typically involve?
The basic methods of ransomware attacks have remained the same over the course of time. During a typical attack, malware is infiltrated into a network, which then identifies and encrypts critical files, making access and operations impossible for the victim. Then, the attacker demands a ransom to be paid in exchange for the decryption key that reestablishes access to the data. After regaining possession of the data, the ransomware recovery can start.
However, ransomware attacks did change by making the basic procedure more complex – and successful – by adding the threat of exfiltrating data. This involves the public exposure or selling the stolen data for further malicious purposes. While in the case of a traditional attack, a company could just go back to the most recent backup and get rid of the ransom demand, the exfiltration threats make the demand harder to ignore.
How long does it take to recover from a ransomware attack?
How fast ransomware recovery can happen depends on the level of preparedness of the company, backup restoration, and the measure in which the attack impacted the organization. The average downtime after an attack was 18.71 days in 2023. The impact is primarily influenced by whether or not an organization has a data recovery plan.
What’s the price of a ransomware attack?
In 2021, a ransomware demand was $70 million. Since then, the sum reached up to $240 million. And this is only the ransom demand. The rising costs of data breaches reached $1.85 million in 2023. The cost can vary depending on the type of ransomware, but it can also be influenced by whether the data was corrupted or not or if the company has access to the decryption keys or not.
Additionally, even if everything is restored to an operational state, and there’s no more loss on downtime, further steps are necessary that can cost a company a lot of money. Carefully examining the situation to discover the vulnerabilities in the system that caused the attack in the first place and implementing strengthened security measures to prevent future events can be very expensive.

Your money or your life: should you pay in the hope of a fast ransomware recovery?
To pay or not to pay a ransom demand is a hard decision for most businesses, especially if they are caught unprepared. Ransom prices are high; however, the price of downtime can be even higher.
Pros of paying
Most ransomware attack victims who decide to pay the demanded fee do it in the hope of returning to normal operations as soon as possible. For many firms, the cost of downtime can be prohibitive, and minimizing the length of the disruption is paramount. Depending on the magnitude of the problem, paying the ransom can seem like the more minor bad in the equation. If files have been encrypted or corrupted, getting a backup going to make systems operational again can cost tremendous amounts of money. Giving the criminals what they want and starting ransomware recovery as soon as possible can look like the only solution.
Additionally, other damages are involved, which can require more than money and time to be corrected. Modern ransomware attacks include an element of blackmail to make sure they get paid. The method is called double extortion, when hackers threaten to exfiltrate critical information that could compromise the firm’s reputation. To avoid being exposed and protect their reputation, some organizations end up deciding to pay.
Cons of paying
Firstly, there’s no guarantee that the hackers will play fair and grant access to the encrypted data. According to Statista, about 25% of the victims didn’t get their data back after payment. Also, even if you do get the data back, it can be corrupted. Statistically, you can quickly end up in a situation where you’re facing the costs of ransomware recovery, and paying the ransom doesn’t have any positive outcome at all. Considering the worst-case scenarios, taking the leap of faith might not be worth it.
Secondly, a company can become a target repeatedly if criminals see it as an easy target. According to a study by Cybereason, 80% of the queried organizations were attacked a second time after paying the ransom. Knowing that they can make easy money on you, it’s highly unlikely that cybercriminals will back down. Experiencing a second attack can make ransomware recovery even more complicated.
Paying can result in civil penalties
The US government can penalize organizations that pay ransom demands.
In 2020, the US Treasury Department’s Office of Foreign Assets Control, or OFAC, included ransomware attackers in its program to sanction malicious cyber-activity. Paying a ransom can count as offering financial assistance for cybercriminal activity, and as such, it can be subject to civil penalties by the OFAC. Also, the penalty is applicable, even if the organization doesn’t know that they are dealing with a person or an organization subject to US sanctions.
Ransomware recovery practices
According to Security Magazine, in 2023, a cyberattack occurred every 39 seconds. With the growing number and sophistication of threats, preparing for an attack with a detailed ransomware recovery plan is becoming non-negotiable.
Having a ransomware recovery plan
A ransomware recovery plan is a written, step-by-step guide for the course of action to take in case of a ransomware attack. It typically makes part of an extensive disaster recovery plan and includes a plan of action for the organization that should be followed strictly. It includes preventative measures for recognizing anomalous activity and measures for monitoring and handling critical data.
Additionally, it has prioritized instructions on how to act after the malicious infiltration is recognized. It names a person responsible for handling the situation and assigning roles and responsibilities to teams in the ransomware recovery process. The individual accountable for the response and recovery strategy is also responsible for ensuring that the organization complies with local data protection laws.
Recovering encrypted files
So, you want to get the files back but decide not to pay the ransom. It is possible to go back to the last backup and continue. However, it can be a lengthy and challenging process, and it can only happen with an efficient data backup plan in place. Also, cybercriminals can directly target this strategy with methods like injecting malware into the system or compromising backup restoration.
The bad news is that without the backups, recovering data after it has been compromised can’t be guaranteed, even if the authorities take down the cybercriminal organizations. Sometimes, the decryption keys cannot be recovered, rendering companies helpless and significantly delaying ransomware recovery.
Handling the Double Extortion tactic and repeated attacks
The best way to deal with the double extortion technique is to take preventive steps before it happens. ADX and machine learning tools can be valued allies for companies in detecting unusual activities and blocking criminal attempts to steal data. If a hacker gets into the system, running the double extortion attack can at least be prevented, shortening the ransomware recovery process. Implementing these precautionary measures extensively on devices can help organizations secure a line of defense against the worst-case scenario.
Conclusion
Statistically, 60% of small businesses are doomed to shut down in six months after experiencing a major data breach or cyberattack. Experiencing an attack unprepared can wreak havoc on a company, and failure to recover the data can lead to a permanent shutdown. For this reason, a ransomware recovery plan is crucial for all organizations, especially those operating from finite funds.
Sooner or later, ransomware attacks happen. It’s paramount that when it happens, your company is prepared, and a ransomware recovery plan is there to cushion the fall.
Got questions? Want to talk specifics? That’s what we’re here for!
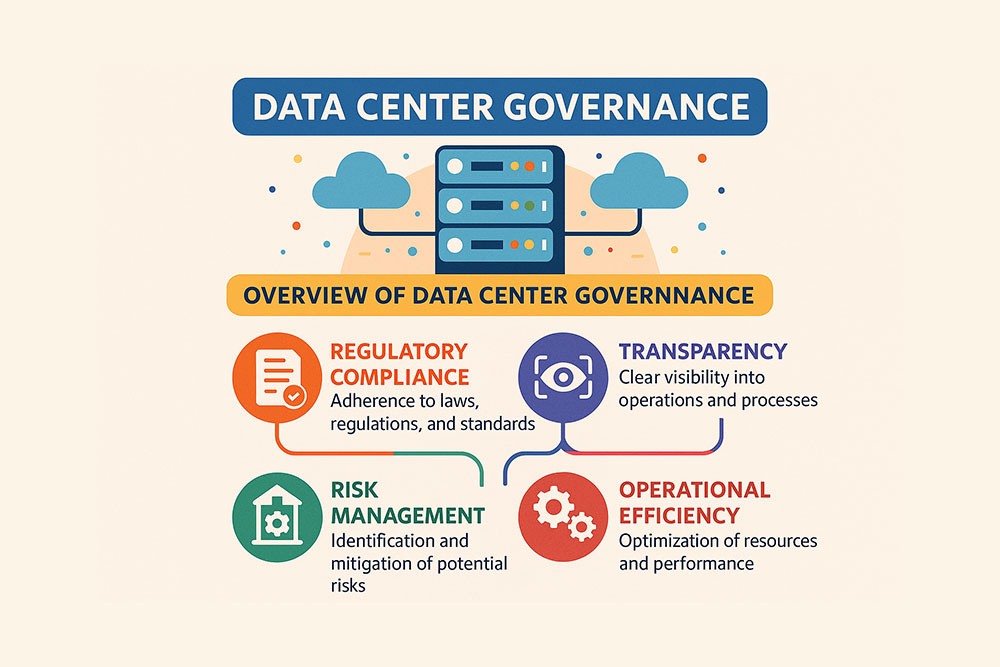
Discover how Volico Data Centers can help your organization with protection against the growing number of cyber threats. Learn how our comprehensive managed security services, disaster recovery, and business continuity solutions can help prevent disasters.
• Call: (305) 735-8098
• Chat with a member of our team to discuss which solution best fits your needs.