
The Complete Guide to Data Center Redundancy and Tier Classifications
Reliability is one of the major ongoing goals of data center operators. Several circumstances have to be in place, and with the rapid technological advancements,

Reliability is one of the major ongoing goals of data center operators. Several circumstances have to be in place, and with the rapid technological advancements,

For strictly regulated industries, there’s nothing more important than ensuring that data is safe and secure. Data security and compliance are the first concerns for
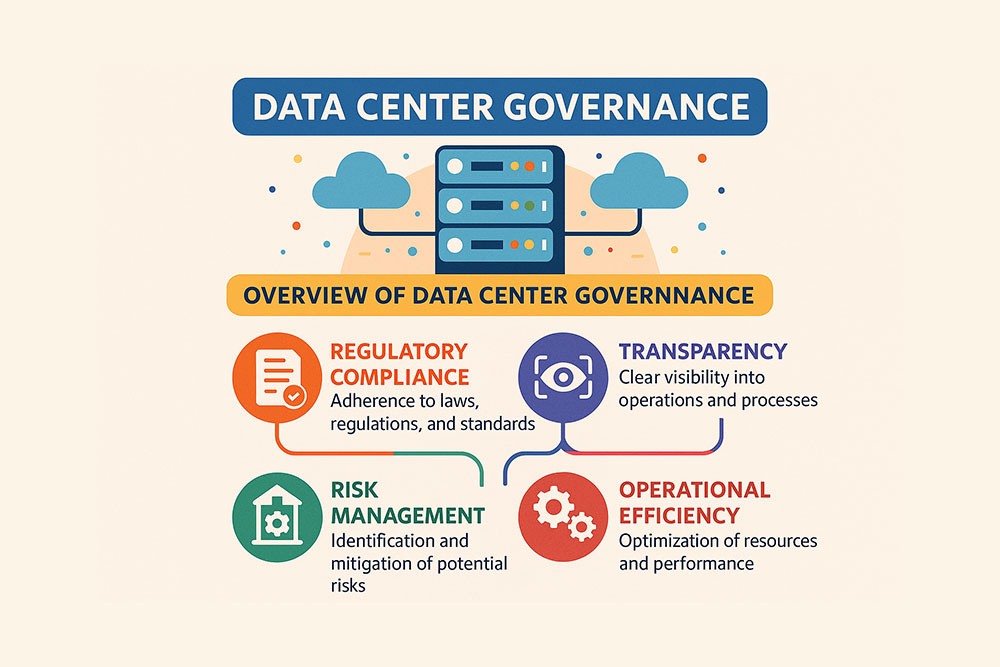
Data center governance is a term that doesn’t ring as many bells as the similar “data governance” does. Nevertheless, its importance, driven by the need

Organizations today are increasingly relying on multiple different service providers for their many different needs. We have IaaS providers and SaaS providers to cover everything

Some might think compliance is just another item to tick off on a list; however, in reality, it’s about much more than that. Data center

Should you buy or partner with a SOC to meet growing cybersecurity demands? Or should you build your own Security Operations Center (SOC)? The purpose

The amount of data healthcare churns per second is almost incomprehensible. Further, research by RBC capital markets forecasts that the compound annual data growth rate
Volico Data Centers is proud to announce the completion of the SOC 2 Type II audit for 2019. A-LIGN, an independent accounting, and auditing firm

Last year saw a sharp increase in the number and impact of cyber attacks on educational institutions across the US. While healthcare and financial industries

The General Data Protection Regulation (GDPR) of the EU and the Health Insurance Portability and Accountability Act (HIPAA) of the United States are two critical
About cookies on Volico.com
Volico Data Centers use cookies to collect and analyse information on site performance and usage. This site uses essential cookies which are required for functionality. More detail is available in our privacy policy. Learn more