Should you buy or partner with a SOC to meet growing cybersecurity demands? Or should you build your own Security Operations Center (SOC)?
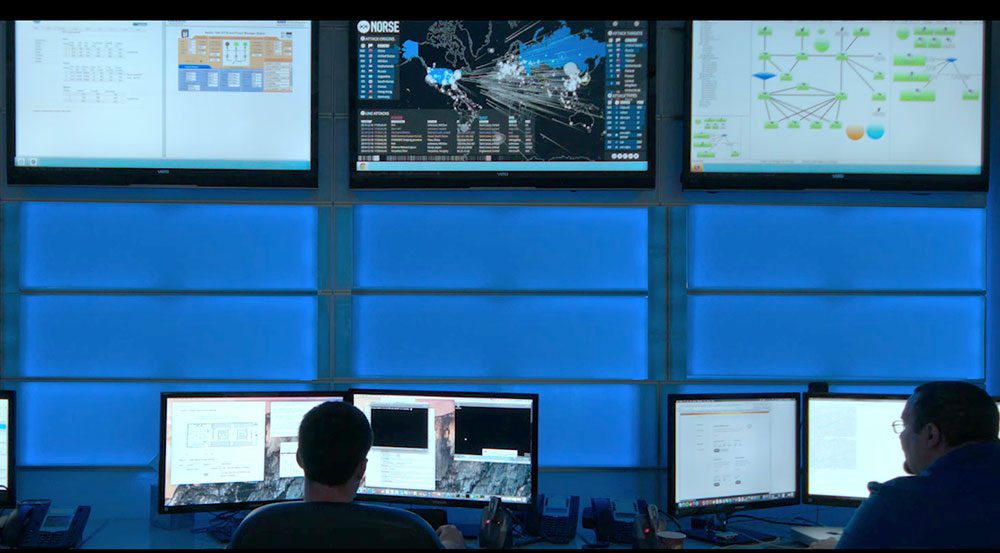
The purpose of the security operations center (SOC) is to constantly monitor, prevent, detect, investigate, and respond to cyber threats 24/7. Therefore, security operations centers have become an essential element of threat detection.
An organization has complete control over security incidents monitoring by having their in-house SOC (Security Operations Center). With an internal SOC, an organization can tailor the security operations to meet better the requirements of the different divisions and teams. These advantages come at a cost, and many organizations outsource their security operations to managed services providers (MSPs).
Keeping up with cybersecurity threats may seem impossible when your business lacks cybersecurity resources. Using a SOC to fill in the gaps is a logical solution, but do you need to build your own SOC, or are there other options?
The Security Operations Center (SOC) is the core foundation of an organization’s cyber security program. The SOC holds important resources, tools, processes, and people that the company utilizes to detect and protect against cyber threats.
Whether it’s sourced internally or externally, an organization must implement its SOC to possess these essential capabilities. This blog dives into the pros and cons of SOC outsourcing, discussing and examining the differences between both aspects, and will help you decide which one is better to suit your organization.
Understanding the Pros and Cons of In-House Security Operations Center (SOC)
- 24/7 Network Monitoring: Cyber threats are a constant vulnerability to a company since they may occur anytime outside of regular business hours. Subsequently, a SOC must be able to provide detection and response protection all day, every day.
- Incident Response Capabilities: Detecting a cyber security threat is important; however, it is crucial that a company’s SOC, whether internal or external, has the ability to respond properly to the incident.
- Threat Hunting: Nowadays, it is hard to be certain that companies have zero vulnerabilities to various cyber threats and attacks. Therefore, it is necessary for an organization to proactively search for internal threats within a network that may be hidden.
- Compliance Management: All businesses are subject to be compliant with data protection regulations which include protecting sensitive data from unauthorized access. The responsibility of a SOC is to demonstrate regulatory compliance and protection of sensitive data.
Internal or Outsourced Security Operations Center?
Undoubtedly, every company is a potential target of cyber attacks. However, the major difference between potentially dangerous and mitigated attacks is the effectiveness and strength of the company’s Security Operations Center.
Recently, as organizations have begun to realize that they lack sufficient resources to defend against cyber attacks, outsourcing a SOC has become increasingly popular. It is paramount to consider whether an internal or external SOC will best suit your company’s needs.
Internal SOC Advantages
Essentially, the biggest advantage of maintaining an internal SOC is that the company has complete control and does not need to rely upon a third-party provider.
- Sole Expertise: Being the sole operator of their SOC, a company has security experts devoted to protecting their network alone. Increased familiarity and comfort with the systems are keys to success that may be difficult to find elsewhere.
- Internal Data Storage: The option of storing all private files and security data on-site helps a business maintain control and security over its data.
- Customizable: Full control means a company can operate its security solutions however they most desire.
Internal SOC Disadvantages
The limitations, however, of having complete control and no dependency on a third-party provider can be the difference in how secure an organization truly is.
- Cost: The resources and tools required to develop an effective and functioning Security Operations Center are expensive. As cyber threats evolve and become more complicated, the technology needed to defend against them must also develop, which can be a large investment.
- Planning and Implementing: Not only is cost a large factor in implementing an internal SOC, but also time plays a huge role in the planning process.
- Trained Experts: There is a shortage of trained cybersecurity experts in the field. So, even if a company can implement its own SOC, finding trained experts to run it may be challenging.
Outsourcing SOC Benefits
- Simplifies Infrastructure Design: Implementing and maintaining an internal Security Operations Center pose many difficulties.
- Easier to Manage Costs: SOCs can become costly when implemented internally; however, externally, these costs become distributed.
- Accessibility to Cybersecurity Experts: As cybersecurity specialists are hard to find these days, a company can have immediate access to experts in the field in case of a cybersecurity threat.
- Scalability and Flexibility: Outsourcing your SOC relieves the burden of overseeing cyber threats since they will already be handled by a provider.
- Active and improving Threat intelligence: With access to multiple threat research databases, an external SOC provider can supplement internal data analytics to benefit the customer’s security.
- Department Collaboration: The environment created when outsourcing SOC will establish more clear and defined roles within the cybersecurity team and eliminate conflicts of interest between various departments.

Outsourcing SOC Drawbacks
- Data Storing Vulnerability: When stored externally, the organization has less control over the security measures taken by the SOC providers to ensure the safety and security of their data.
- No Dedicated IT Security team: IT security is a critical component of an organization. Without SOC, there is essentially no IT security team internally to protect and defend against cyber attacks.
- Limited Knowledge of Business Needs: External Security Operation Centers are tasked with protecting many organizations and, therefore, may not have the bandwidth to provide a unique sense of understanding of a company’s specific business necessities.
- Finite Customization Options: Depending on budgets and needs, customizable SOC options are limited.
Selecting the Right SOC Provider
As cyber threats continue to evolve, they pose new and difficult challenges. How can organizations effectively defend against them? The answer lies within internal and external Security Operation Centers.
Choosing between an internal and outsourced SOC is an essential first step for an organization designing its security program. Both options have pros and cons; the right choice can depend on an organization’s unique situation and conditions.
Contact us today for a no-cost consultation if you are considering hiring an outsourced SOC and reputable MSSP. Get in touch with some of the most experienced professionals in co-managed security systems, then you should contact us. We have experience in security systems across all company sizes and industries.
Volico has successfully completed HIPAA, SSAE16, SOC 2 Type II, and NIST audits compliant. A SOC2 certification consists of multiple procedures and policies in place to ensure your data is appropriately handled and secured. Volico’s data centers are SOC2 Certified and immediately ready to handle your compliant hosting needs.
Discover how Volico can help you with your Managed Security needs.
• Call: 888 865 4261
• Chat with a team member to discuss which solution best fits your needs.
This blog article was written with a contribution by Emma Sasonov, Tufts University Student. View Full Bio »